The digital economy of 2026 has reached a turning point. For years, businesses relied on public cloud systems for convenience and scalability, but that came at a hidden cost: the loss of control over proprietary data. As AI systems aggressively harvest data for training, organizations are realizing that traditional models are no longer sufficient.
By shifting to sovereign infrastructure, enterprises regain full ownership of their data, infrastructure, and digital operations. Instead of depending on shared environments, they operate within secure, private ecosystems. This is no longer just about security; it is about building a future where businesses can innovate without fear of exposure.
The Evolution of Data Ownership and Sovereign Infrastructure
Over the past decade, the risks associated with shared environments have matured alongside the technology.
According to McKinsey’s State of AI 2025, 51% of organizations using AI have already experienced at least one negative consequence, with privacy, regulatory compliance, and explainability among the top risk categories organizations are increasingly working to mitigate.
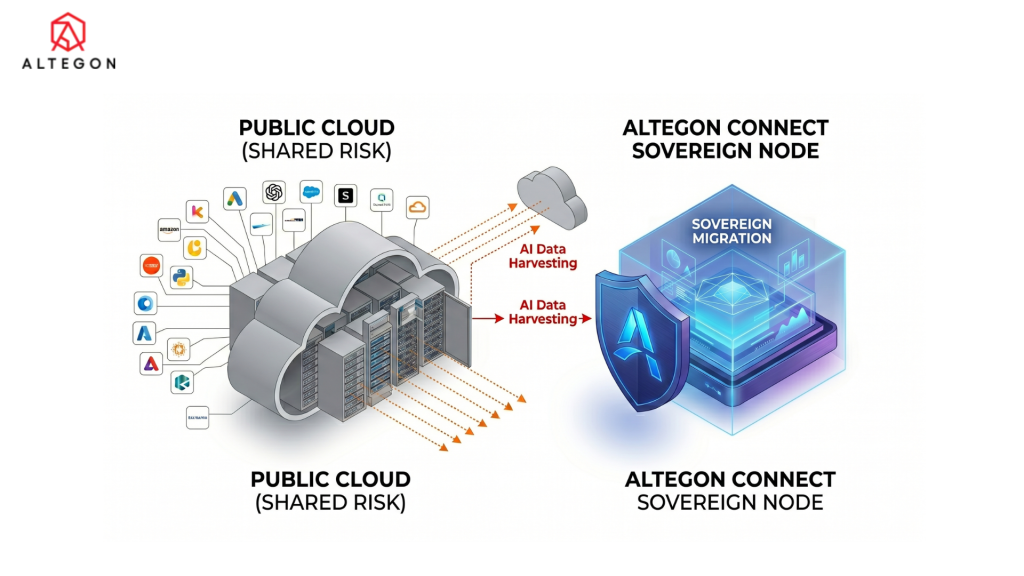
Many organizations are now questioning how their data is being used. Even when labeled as “anonymized,” data is often analyzed to train third-party AI systems. This creates a critical vulnerability: your intellectual property could indirectly support your competitors’ innovations. With sovereign infrastructure, businesses eliminate this uncertainty by building private environments where every piece of data is fully controlled. For a deeper look at how this impacts your broader tech stack, refer to our enterprise tech sovereignty guide for 2026.
The Public Cloud Vulnerability Gap
Public cloud systems operate on a shared responsibility model, which often leads to gaps that attackers exploit. Common risks include:
- Multi-tenant exposure: Where a single breach impacts multiple users.
- Misconfigured security: Leading to accidental data leaks.
- Persistent external access: Where providers retain access for “monitoring,” creating a privacy gray area.
In contrast, sovereign systems operate within a closed environment. This is why many enterprises are moving from SaaS video platforms to sovereign communication infrastructure to ensure their most sensitive internal discussions remain private.
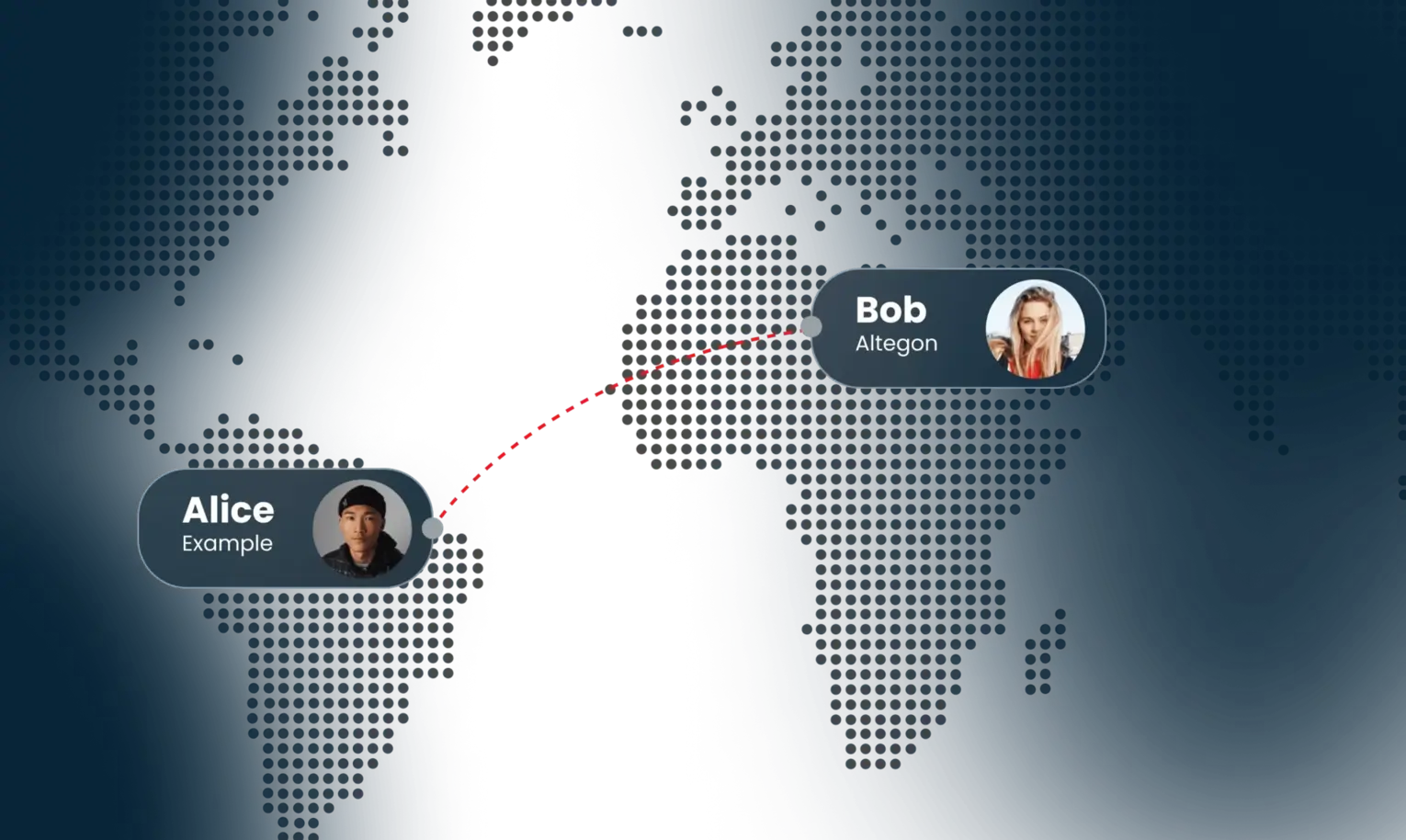
Achieving Sovereign Flow in Professional Environments
Security alone is not enough; performance also plays a crucial role in modern business operations. Public cloud platforms often introduce limitations such as latency, server congestion, and usage restrictions. These issues can disrupt workflows and reduce productivity.When teams don’t have to worry about technical constraints, they can focus on customer experience trends for 2026 to drive growth.
Sovereign environments solve this problem by enabling what can be described as “Sovereign Flow.” This means:
- Seamless collaboration without interruptions
- Stable performance without external interference
- Freedom from artificial limitations
Because businesses control their own infrastructure, they can optimize it according to their specific needs. As a result, teams can focus on innovation and decision-making instead of dealing with technical constraints.
How Altegon Helps You Achieve Sovereign Infrastructure

At Altegon, we understand that transitioning to a sovereign model requires both strategic planning and technical expertise. Therefore, we provide a complete framework that enables businesses to move from public dependency to private control without disruption.Our core solution, Altegon Connect Sovereign Node, offers:
Dedicated Sovereign Nodes
Altegon deploys private cloud environments where your organization maintains full ownership of its data. These nodes provide the scalability of modern systems while ensuring complete isolation from shared infrastructures.
Zero External Access Architecture
We eliminate unnecessary external access points. Because your data remains within a controlled environment, the risk of breaches or unauthorized access is minimized.
AI Data Protection
Altegon ensures that your proprietary data is not used to train external AI models. This protects your intellectual property and prevents competitive leakage.
Unrestricted Performance
Without the congestion of shared servers, your operations run smoothly. This leads to consistent performance, improved collaboration, and higher productivity.
By choosing Altegon, organizations gain not just a platform but a long-term strategy for secure and efficient digital operations.
The Strategic Advantage of Private Nodes
Data sovereignty has moved from a compliance checkbox to a board-level competitive variable. In regulated industries – healthcare, financial services, government, the ability to define full chain-of-custody over sensitive data is now a prerequisite for enterprise contracts, not a differentiator. Clients and partners are increasingly conducting security due diligence before signing and shared-infrastructure answers no longer satisfy procurement teams.
The financial exposure is equally concrete. The IBM Cost of a Data Breach Report 2024 puts the average breach cost at $4.88 million globally, with breaches in healthcare averaging $9.77 million – the 14th consecutive year healthcare ranked as the costliest industry. Beyond direct costs, organisations operating on shared infrastructure face compounding risks: regulatory fines under GDPR (up to 4% of global annual turnover), reputational damage and loss of client trust that rarely fully recovers.Shared infrastructure can no longer satisfy procurement teams who are increasingly skeptical of standard AI meeting platforms that don’t prioritize sovereignty.
Transitioning from Legacy Systems to Sovereign Models

The most common barrier to sovereign infrastructure is not technical, it is organizational inertia. Existing contracts, sunk costs in public cloud tooling, and the perceived disruption of migration lead many IT leaders to defer the decision. The risk of deferral, however, is compounding.
Global data protection regulations are tightening across every one of Altegon’s core markets. GDPR enforcement actions in the EU have accelerated. Saudi Arabia’s PDPL came into full effect with active enforcement. In the United States, HIPAA scrutiny has intensified as healthcare AI use cases expand. Organisations still operating on shared public infrastructure are building compliance debt that becomes progressively harder to unwind.
A well-scoped migration to a sovereign model does not require a full infrastructure overhaul overnight. Organisations typically begin by identifying the highest-risk data categories – communications records, client data, proprietary AI outputs and migrating those workloads first. With the right deployment partner, this can be executed in phases without disrupting live operations. The organisations that begin this transition now will have a measurable compliance and reputational advantage over those that wait for a forcing event.
Conclusion!
As the digital landscape continues to evolve, control over data is becoming more critical than ever. Sovereign Infrastructure provides a secure, reliable, and future-ready solution for enterprises that want to protect their intellectual property and maintain full ownership of their operations.
Public cloud systems may have defined the past decade, but the future belongs to organizations that prioritize sovereignty, privacy, and performance. By investing in private infrastructure today, businesses can secure their competitive advantage for years to come.
If you are ready to take control of your data and eliminate external risks, now is the time to explore sovereign solutions with Altegon.
Protect your Intellectual Property Before It Becomes Someone Else's Training Data.
As global compliance standards tighten and breach costs escalate, the cost of waiting is higher than the cost of switching. Secure your enterprise’s future today.
See Altegon’s Sovereign Node in Action
FAQs
1. What is Sovereign Infrastructure?
It is a system where businesses fully control their data, infrastructure and operations within a private environment, eliminating reliance on shared public systems.
2. How does it improve data security?
Because data stays within a controlled ecosystem, there are no external access points, which significantly reduces the risk of breaches or unauthorized use.
3. Can businesses easily switch to sovereign systems?
Yes. With the right strategy and support, organizations can transition smoothly without disrupting their daily operations.