The strategic priority for IT leaders in 2026 has evolved toward Direct Data Ownership. While the previous decade was defined by the rapid adoption of public cloud, mature organizations are now moving toward sovereign infrastructure to secure long-term financial predictability and full institutional control over their intellectual property.
Industry-wide directional trends, as highlighted in recent Gartner and IDC analysis on infrastructure repatriation, show a growing movement of high-bandwidth workloads specifically video back into controlled environments to bypass the complexities of the “shared responsibility” security model.
The Strategic Drivers of Video Repatriation
The transition toward sovereign infrastructure is a calculated response to four distinct institutional pressures facing the modern CIO.
1. Financial Predictability: Managing Infrastructure Costs
Modern IT decision-makers are prioritizing repatriation to solve the challenge of unpredictable cost spiraling often associated with public cloud scaling.
- Removing Egress Fee Volatility: Public cloud providers charge to move data out of their ecosystems. For high-bandwidth video, these “toll fees” can reach tens of thousands of dollars annually. Sovereign hosting removes these unpredictable costs.
- The Scaling Advantage: Sovereign infrastructure allows managers to shift from volatile OpEx to stable, asset-based CapEx. This ensures the monthly budget remains fixed, regardless of user growth or data volume.
2. AI Sovereignty and Data Integrity
Sovereign hosting ensures that the intellectual property generated in meetings remains within infrastructure your organization controls entirely.
- Private AI Deployment: IT leaders are utilizing Private LLMs to generate automated meeting summaries and actionable insights without sensitive footage ever leaving their physical control.
- Integrated Intelligence: By keeping transcription and indexing internal, organizations ensure that audio data is never routed through third-party productivity tools, significantly reducing the external attack surface.
3. Latency: Optimizing for LAN Performance
By hosting locally, traffic remains on the Local Area Network (LAN). This ensures true 4K resolution for in-office participants and maintains high performance independent of external connection quality.
4. Regulatory Compliance and Residency Requirements
The 2026 regulatory landscape has made “documented residency” a legal necessity. For a detailed breakdown, see our HIPAA vs. GDPR video conferencing compliance guide.
- Direct Control: For FinTech, Healthcare, and Government sectors, maintaining physical control over storage is the primary path to meeting strict audit requirements.
- The 2026 Audit Standard: Sovereign environments provide the immutable logs and physical key management required for modern transparency standards.
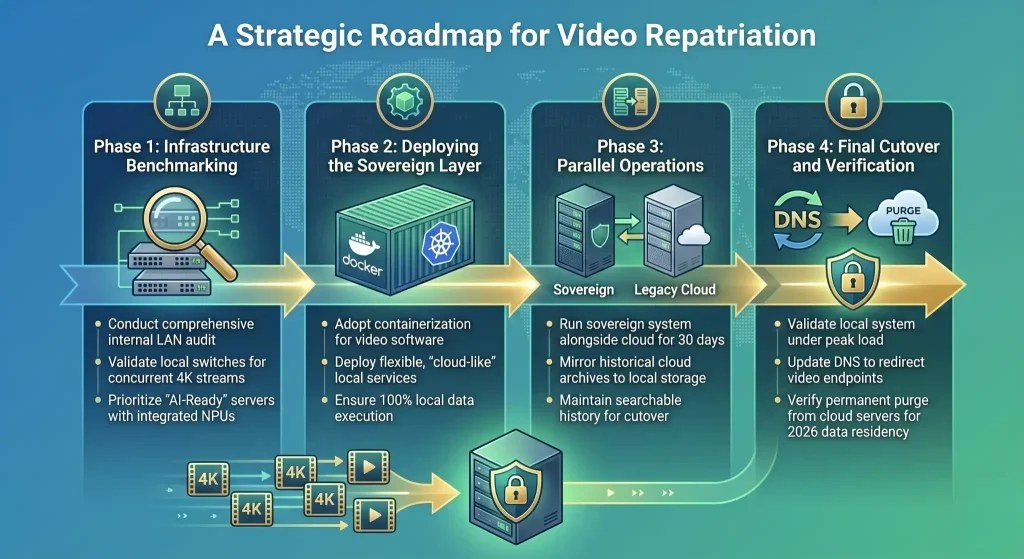
A Strategic Roadmap for Video Repatriation
Transitioning video infrastructure requires a phased approach to ensure high availability and data integrity.
Phase 1:
Infrastructure Benchmarking Audit internal LAN capacity to ensure local switches can handle concurrent 4K streams. Hardware selection should prioritize AI-Ready servers with integrated NPUs for local transcoding.
Phase 2:
Deploying the Sovereign Layer Utilize containerization (Docker, Kubernetes) to deploy video software. This provides cloud-like flexibility and ease of updates while ensuring all data execution remains within your private environment.
Phase 3:
Parallel Operations Run the sovereign system alongside the legacy provider for 30 days. Mirror historical cloud archives to local storage arrays to ensure searchable history remains intact before the final cutover.
Phase 4:
Final Cutover and Verification Once the local system is validated under peak load, update DNS to redirect endpoints. Finally, verify that data has been purged from the cloud provider’s servers to fulfill 2026 residency obligations.
Technical Comparison: 2026 Outlook
|
Feature |
Public Cloud Hosting |
Sovereign Infrastructure |
|
Financial Model |
Variable OpEx (Per-user/Egress) |
Fixed CapEx (Asset-based) |
|
Data Privacy |
Shared Responsibility Model |
Full Institutional Control |
|
Performance |
WAN-dependent (Variable) |
LAN-speed (Near-zero Latency) |
|
AI Integration |
General/Third-party Models |
Custom Private LLMs |
|
Auditability |
Limited Provider Logs |
Immutable Audit Trails |
Conclusion: From Tenants to Architects
The shift toward sovereign video hosting in 2026 is not a regression to the past; it is an evolution toward Data Ownership. Choosing sovereign infrastructure is a strategic move for organizations that prioritize intellectual property security, regulatory audit readiness and predictable cost structures.
Altegon Connect’s Sovereign Node plan is built specifically for regulated industries HIPAA, GDPR and Saudi PDPL ready offering full infrastructure control and BAA support.
Ready to take full ownership of your video infrastructure? Book a Demo with our Infrastructure Team.
Frequently Asked Questions
Q1: Does sovereign hosting require more manual maintenance?
No. Modern sovereign platforms use containerized architectures that allow for automated updates and remote monitoring, providing the ease of SaaS with the security of private hardware.
Q2: How does repatriation support GDPR and HIPAA compliance?
It simplifies compliance by removing the “Third-Party Data Processor” risk. It ensures data residency stays within your jurisdiction and provides the immutable audit logs required for GDPR’s 72-hour supervisory notification and HIPAA’s 60-day breach notification obligations.
Q3: Can we still use AI features if we move off the public cloud?
Yes. Sovereign infrastructure allows you to run Sovereign AI local instances of LLMs that process meeting data internally without sending it to public servers for training.
Q4: Is “On-Premise” considered a legacy approach?
Quite the opposite. 2026 sovereign technology is more advanced than legacy cloud, utilizing private WebRTC media servers within your own environment to provide a high-performance, “bank-vault” security environment that public clouds cannot replicate.